Beyond SOC 2: Why IRAP Should Be the De-Facto Standard in Supplier Assurance
Our thoughts on why IRAP should become the de-factor standard in supplier assurance, and how GRC Platforms have shifted the SOC 2 goal posts (closer and wider).
Written by: Hareen Siriwardena
05 March 2026
Beyond SOC 2: Why IRAP Should Be the De-Facto Standard in Supplier Assurance
Security questionnaires once dominated third-party assurance. They were often completed by commission driven sales teams and reviewed superficially. To improve rigour, many organisations turned to independent attestation frameworks, most notably SOC 2. Today, SOC 2 reports are widely accepted as the default that security maturity has been externally validated.
However, as SOC 2 adoption has scaled, it has also been industrialised. Automation platforms now promise rapid SOC 2 readiness, continuous monitoring, and evidence collection via APIs. This shift raises an important question. Is SOC2 still a credible indicator the organisation has implemented reasonable security controls?
What SOC 2 Type II Actually Assesses
A SOC 2 Type II report is issued under the AICPA Trust Services Criteria. It evaluates whether a service organisation has designed and operated controls effectively over a defined period, typically six to twelve months. Assessments can cover one or more of five domains: security, availability, confidentiality, processing integrity, and privacy.
A SOC 2 report generally includes:
- A description of the system and its boundaries
- Infrastructure and hosting details
- Data flow and architecture summaries
- Independent auditor testing of selected controls
- Exceptions or deviations
- Complementary User Entity Controls (CUECs), which outline responsibilities that customers must implement themselves
The vendor defines the scope of a SOC 2 assessment by defining the controls they have implemented to meet the trust services criteria. This flexibility enables efficiency, but it also introduces variability in depth and coverage.
Historically, SOC 2 audits were labour-intensive. Evidence collection involved manual screenshots, policy reviews, ticket samples, interviews, and configuration exports. Auditors needed to understand the system architecture and operational environment to validate the effectiveness of controls. While costly and time-consuming, this process created meaningful friction, and therefore meaningful assurance.
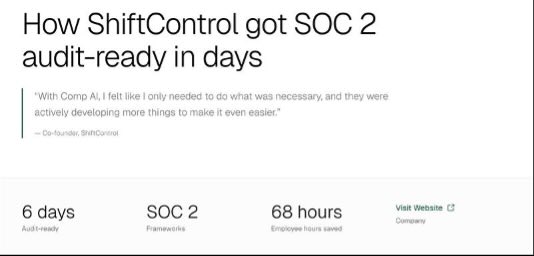
Today, compliance automation platforms are transforming delivery models. Many now provide continuous control monitoring, API-driven evidence ingestion, automated screenshots, infrastructure scans, and templated policies. Some vendors claim SOC 2 readiness in as little as six weeks or even days…
These efficiencies are valuable. However, they also shift effort away from architectural understanding toward evidence orchestration. Previously, SOC 2 assessments were a thoughtful process where an audit firm would define the controls and processes. Now GRC platforms assume a base set of controls based on the SaaS that is being run, and the cloud platform used (Azure, AWS, GCP), avoiding specific organisational nuances and processes. When assurance becomes highly standardised and tool-driven, depth can suffer. The risk is that a SOC 2 report becomes a procedural milestone rather than a robust validation of system security.
What an IRAP Assessment Involves
An IRAP assessment is an independent security evaluation conducted by an ASD-endorsed assessor against the Australian Signals Directorate Information Security Manual (ISM). The ISM contains approximately 1,000 prescriptive controls covering governance, technical security, personnel practices, physical security, supply chain management, secure development, networking, and cryptography.
Unlike SOC 2, IRAP assessments are not limited to control documentation and operational testing. They require assessors to develop a deep understanding of:
- Defined system authorisation boundary
- System Architecture
- Data flows and integration points
- Hosting environments and inheritance
- Threat exposure
IRAP assessors validate the implementation of controls in the operational context. They examine whether controls are effectively engineered, not just documented. Governance structures, risk management practices, personnel security processes, and secure software development life cycles are all scrutinised.
This broader lens ensures assurance is not confined to the SaaS product itself but extends to the organisational practices that support it.
The Automation Illusion
Modern compliance tooling has created a perception that assurance can scale infinitely. However, if suppliers use identical tooling, collect identical evidence, and test identical configurations, assurance becomes standardised without contextual grounding.
Automation can introduce concentration risk. Uniform approaches may overlook unique architectural weaknesses or business-specific threat exposures.
IRAP retains a human analytical layer. Assessors apply professional judgement to architecture, boundary definitions, and risk treatment decisions. This judgement is difficult to replicate solely through automation.
For organisations protecting sensitive or classified information, this analytical layer matters. The question is not whether a control was monitored continuously—it is whether the system is defensible against real-world threats.
Accelerating IRAP Without Diluting Assurance
While IRAP cannot be fully automated, it can be accelerated. Modern GRC platforms can reduce documentation friction and improve assessment readiness by enabling:
- Clear and accurate control implementation statements
- Centralised enterprise control mapping
- Effective control inheritance across systems and cloud service providers
- Framework currency management as ISM versions evolve
These capabilities streamline preparation without undermining assessor scrutiny. They help organisations present coherent, accurate, and maintainable control narratives—reducing rework while preserving rigour.
The goal is not to replace the assessor. It is to ensure the system is genuinely ready for deep validation.
Matching Assurance to Risk
For high-risk environments, where sensitive, regulated, or government data is involved, SOC 2 addresses only part of the supplier risk equation.
IRAP assessments deliver:
- Deeper technical validation
- Broader organisational assurance
- Stronger architectural scrutiny
- Greater resistance to automation dilution
Additionally, IRAP assessors are endorsed by the Australian Signals Directorate (ASD). ASD maintains a detailed Common Assessment Framework, an IRAP Assessment Policy and Procedure as well as detailed reporting templates, providing assurance on the depth and scope of assessments. Select reports are chosen for quality assurance, adding an integrity layer to the ecosystem.
As supplier ecosystems become more interconnected, assurance depth matters more than audit speed. The relevant question is no longer, “Do they have a SOC 2 report?” It is, “Has their system been engineered, assessed, and validated to withstand real-world threats?”
For organisations operating in high-trust environments, IRAP is increasingly the benchmark that answers that question.